Compliance and the Cloud: Debunk the Myths
It is no secret that the benefits of the cloud are enormous. The cloud enables scaling, rapid deployment and provisioning, all of which means that users can enter new markets more quickly and integrate acquired companies easily. And they can do all this while reducing waste, shortening deployment times and more importantly, lowering costs.
But despite the growing numbers of businesses that are adopting the cloud worldwide, there are still some companies that are reluctant to move their workloads to the cloud. This is sadly due to the fact that there are still many negative myths which surround the cloud and compliance in the cloud. It is important to point out that most standards of compliance which govern IT management are not designed with cloud in mind. For example, compliance standards are mostly concerned with maintaining the integrity of data and not locking down entire virtual environments. So, it’s quite easy for companies who look forward to adopting cloud services to be confronted with many questions regarding compliance in the cloud, which sadly remain unanswered…that is, until now.
MYTH #1: Security is Security After all!
When talking about IT infrastructure, security is usually at the top of the list, and for good reason. But when it comes to a regulated environment, you soon find out that there is no such thing as being “good enough”. This is the reason why companies who look to adopt the cloud need to ensure that their data is properly protected. This also means making sure that your network is kept safe from malware and from the prying eyes of cyber criminals.
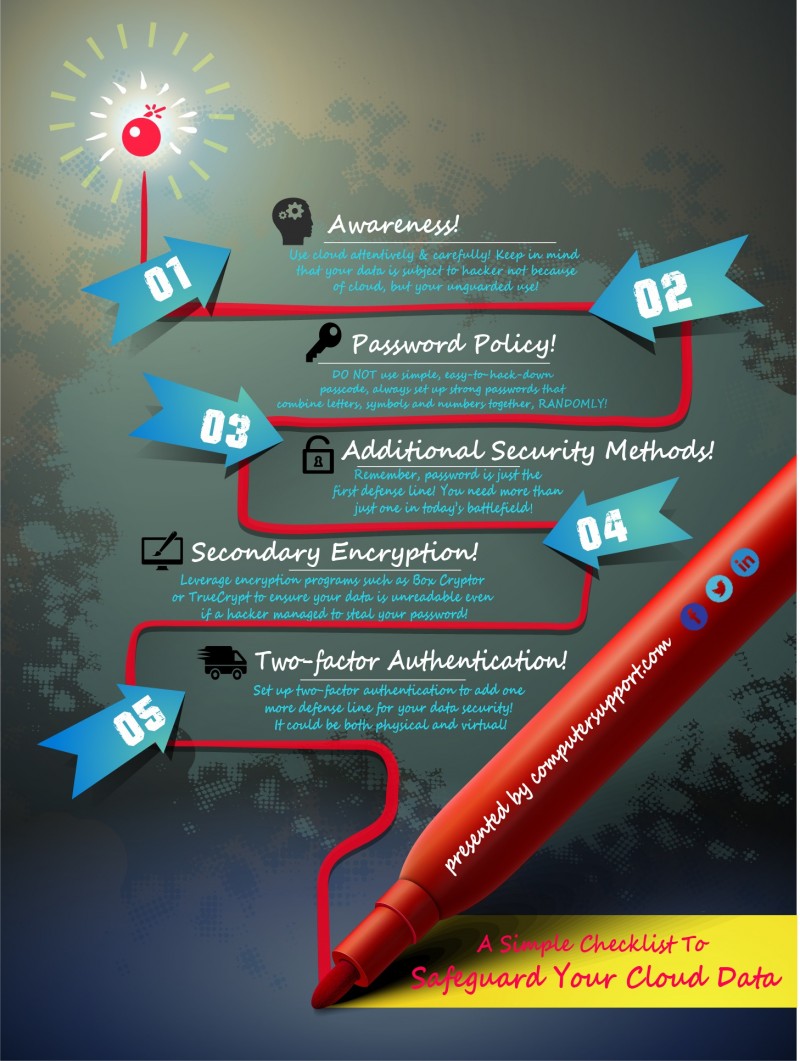
Apart from keeping your antivirus software up-too-date, businesses also need to address the security behavior of their entire organization. This means keeping track of what and how information is being shared? Who has access to data and how that data is being protected from unauthorized access? Do you have network segregation and are you using VLAN tagging? VLAN tagging allows parts of the network to be compartmentalized into distinct VLANs, which enables users to create small quarantine zones between machines and consequently reduces data exposure. When it comes to security, it’s important that you leave nothing to assumption. Here are some tips to make sure your data remains safe on the cloud.
- Use a commercial firewall.
- Use a managed switch which will be able to handle VLANs.
- Invest in a good anti-virus software.
MYTH #2: Get Compliant Capabilities with a Single Vendor
With the increasing interest in compliance in the cloud, many service providers are ready to offer a wide array of compliant capable products. But, unfortunately, the truth is that it is not possible for a single vendor to address the many requirements of various regulatory mandates. In other words, there is really no silver bullet when it comes to compliance in the cloud. So, rather than relying solely on a single vendor (or product), businesses should turn towards implementing a more holistic approach to their security strategy which focuses on the big picture when it comes to the regulatory requirements regarding compliance and the cloud.
It is important to remember that the consumers and not the cloud providers, have to deal with the burden of compliance. And while there might be some grey areas when it comes to regulatory services, it is important for businesses to not hinge their compliance status on a provider who claims to be 100% compliant. Here are a few tips to make sure you get the most bang for your buck when it comes getting compliant cloud services.
- Develop a feasible plan that will help you address any gaps in compliance.
- Work closely with providers and 3rd party vendors to understand the elements of an audit and who those audits are addressed.
No matter how large or small a business, the protection and integrity of data is of utmost importance. Compliance issues in cloud services could lead to loss in sales, fines, and disrupted operations which is the reason why compliance is necessary to thrive in the cloud.