Azure Information Protection: overview & features
Azure Information Protection (AIP) is a Microsoft cloud-based solution that helps organizations classify and protect their documents by specifying appropriate labels. Those can be applied automatically by administrators who define policies, based on relevant suggestions or manually by users.
AIP simplifies data protection by offering a user-friendly solution, while enforcing certain policies and guidelines through visual elements, labeling and Rights Management Service (RMS) encryption.
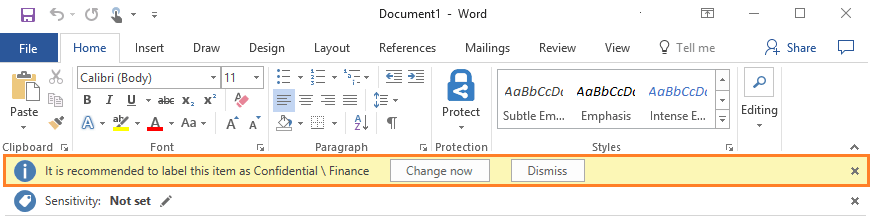
Administrators can configure the labels with rules that detect sensitive data, as for instance credit card information, IBAN or social security numbers etc. When a user types in sensitive data or saves a Word document that contains a credit card number or other sensitive information, the user will get notified by an informative tooltip recommending the right label for the most appropriate classification.
Classify, Label and Protect
Firstly, a document is classified according to a certain level of security such as Personal, Confidential or Classified, either by the document’s author or through automatic labeling. The classification is identifiable regardless of where the data is stored or with whom it’s shared.
Secondly, the right label is applied to the document, based on the security classification that was previously determined.
Finally, labels can be associated with relevant Rights Management Service templates, which encrypt the document and protect it with preset permissions for viewers, readers, authors etc.
Rights Management Service (RMS)
The protection technology solution uses Azure Rights Management. RMS uses encryption, identity, and authorization policies. Similarly to the applied labels, protection stays with documents and emails, independently of the location—inside and outside your organization, networks, file servers, and applications.
RMS is integrated with Office365 and Azure Active Directory. It can also be used with other applications and data protection solutions your organization utilizes on-premise, or in the cloud.
These protection settings can be a part of your label configuration, so that users can both classify and protect documents and emails simply by applying a label. Nevertheless, the same protection settings can also be used by apps and services that support data protection, except labeling. For these applications and services, the information protection settings become available as Rights Management templates.
AIP Latest Features
- Azure Information Protection scanner with its recent updates – In February, Microsoft rolled out The Azure Information Protection Scanner which can be used to discover sensitive information, when they are stored on Windows Server, network-attached drives, or on SharePoint Server data stores. You can specify local folders, UNC paths, and SharePoint Server URLs for SharePoint sites and libraries. The AIP scanner most recent updates include: Start-AIPScan PowerShell cmdlet which can instruct the scanner to start a one-time scan when the schedule was set to manual, after that only new or changed files will be scanned; the ability to create a file types list to include or exclude from scanning, or the ability to search and discover files with sensitive information types without configuring labels for automatic classification which is extremely useful.
- New sensitive information types to help you classify files that contain personal information such as: EU phone number, EU mobile phone number etc.
- ISO standard for PDF encryption, by adjusting the new advanced client configuration.
- Labeling support for Strict Open XML Document format in Word, Excel, and PowerPoint files.
Does your company need professional Azure consulting? Our team of cloud engineers can manage Microsoft Azure for you.


We have used AIP with quite a few of our customers who wanted to have a more secure way of handling documents especially with the introduction of the infamous GDPR.
Glad reading your article! Good process, cheers!